Idax Software is positioned at the centre of a major shift in identity security, driven by Gartner’s introduction…
More

This article was originally published in AM-Online by Aimee Turner. Proportionality bias has led many…
More

Remarketing sector under threat from cybercrime, VRA meeting hears 23 January 2026 Specific weaknesses place…
More

Cybercrime, Psychology, and the M&S Attack Why cyber-crime is con artistry at scale, and what…
More

In environments like Cyber Security, complexity often becomes the default. Messages expand. Value propositions blur.…
More

Hostile cyber activity in the UK is intensifying at an unprecedented rate, posing a direct…
More
What is idax? Overview All you need to know about the idax suite Key Insight…
More
Idax Software, a pioneer in AI-powered identity governance and administration (IGA), announces a dynamic partnership…
More

In today’s digital landscape, organisations face a growing challenge: Ensuring the right people have the…
More

UK Retail seems to be under threat. Recent cyber attacks by Scattered Spider have cost…
More

While most organisations have a robust program in place to protect their technology and information…
More
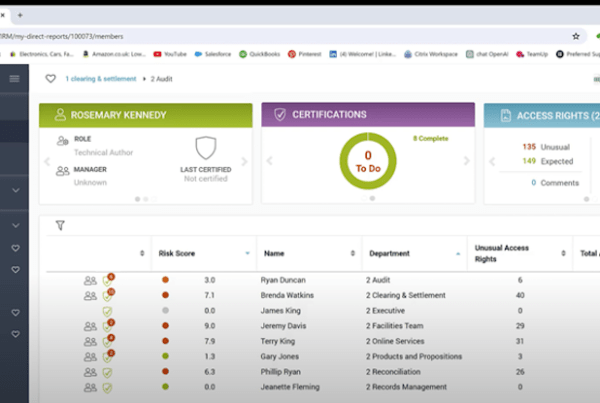
See how you can perform Entitlement Reviews using the idax software suite. https://www.youtube.com/watch?v=tFHW_bYM9ug&t=1s
More


